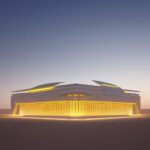
Geopolitical Instability Reshaping Gulf Datacentres and Sovereign AI
The Gulf Cooperation Council (GCC) nations have long positioned themselves as the technological hubs of the Middle East, driven by ambitious visions to diversify their economies beyond oil. Countries like the United Arab Emirates, Saudi Arabia, and Qatar have poured ... Continue Reading →

Securing Student Data After the Canvas LMS Cyberattack
The academic landscape, once viewed as largely insulated from the volatile world of major cyber threats, has been forcefully reminded of its vulnerability. Learning Management Systems (LMS) like Canvas are the digital heart of modern education, housing everything ... Continue Reading →

AWS Outage Drone Strike: UAE Bahrain Attacks Mean for Cloud Security
The digital economy relies on a fundamental assumption: the cloud is immutable. It is a fortress of data, resilient against physical threats and geopolitical instability. However, recent events in the Middle East have shattered this illusion. When AWS Goes Down ... Continue Reading →

Understanding ACME Protocol and Certificate Automation
Not long ago, obtaining a TLS certificate was a bureaucratic ordeal. A system administrator would manually generate a Certificate Signing Request (CSR), submit it through a web portal, wait for email-based domain validation, download the certificate, configure ... Continue Reading →

US Air Force Cloud One Secures $455M Cyber & Automation Boost
The United States Air Force is taking a monumental step forward in its digital transformation journey. In a significant move to modernize its infrastructure, the service branch has secured a massive $455 million contract dedicated to upgrading the Cloud One platform. ... Continue Reading →


