The digital economy relies on a fundamental assumption: the cloud is immutable. It is a fortress of data, resilient against physical threats and geopolitical instability. However, recent events in the Middle East have shattered this illusion. When AWS Goes Down Because of a Drone Strike, the implications ripple far beyond a single region. The attacks on infrastructure in the United Arab Emirates and Bahrain serve as a stark warning to the global technology sector. These incidents highlight the fragility of our interconnected systems and the urgent need to re-evaluate cloud security strategies. As nations prioritize defense against asymmetric warfare, the physical security of data centers becomes as critical as their digital firewalls.
The intersection of warfare and technology has evolved rapidly. Traditional military threats are now directed at critical infrastructure, including power grids and communication hubs. When a drone strike targets a region hosting major cloud providers, the impact is not localized. Cloud providers operate on a multi-region architecture designed for redundancy. However, if a primary hub is compromised, the failover mechanisms can be overwhelmed. The recent attacks in the UAE and Bahrain demonstrate that physical proximity to conflict zones introduces a new vector of risk. Enterprises relying on these regions for latency-sensitive applications face immediate downtime. This downtime is not merely an inconvenience; it represents a loss of trust and potential revenue.
The Reality of Physical Threats to Digital Infrastructure
Cloud security is often discussed in terms of encryption, identity management, and network segmentation. These are vital, but they do not account for physical destruction. A drone strike does not care about your encryption keys. It targets the hardware itself. When the physical servers are destroyed, the data stored on them is lost unless replicated elsewhere. The challenge lies in the replication speed. If the replication lag is too high, data corruption occurs. Furthermore, the power supply to these facilities is often vulnerable. A strike on a substation can take down an entire region’s cloud availability.
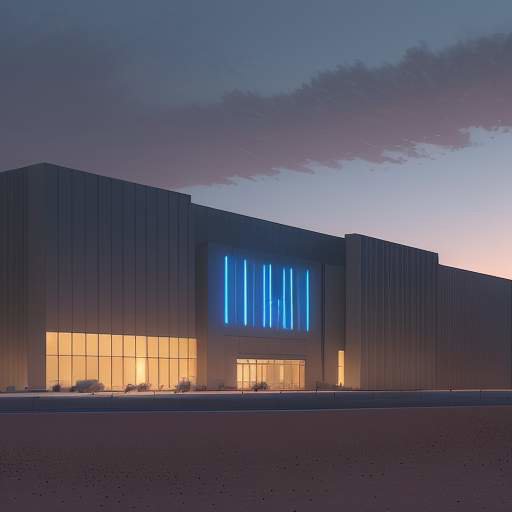
The UAE and Bahrain attacks specifically targeted areas known for hosting hyperscale data centers. These locations were chosen for their connectivity and stability. However, their stability is now questioned. The physical security of these sites must be upgraded to withstand modern threats. This includes hardened perimeters, underground bunkers, and redundant power sources that are independent of the local grid. The cost of such upgrades is high, but the cost of downtime is higher. Businesses must weigh the benefits of low latency against the risks of physical exposure.
How Regional Conflicts Impact Global Data Centers
Global cloud providers do not operate in a vacuum. They are part of a global supply chain. When a conflict erupts in one region, it affects the supply chain for hardware and software. Manufacturers in Asia may face shipping delays if ports are closed. Engineers may be unable to travel to fix issues. The geopolitical landscape is shifting, and cloud providers must adapt. They cannot simply ignore the risks associated with specific regions.
The impact on global data centers is systemic. If a major hub in the Middle East goes offline, traffic is rerouted to other regions. This increases latency for users in those regions. It also increases the load on other data centers, potentially causing cascading failures. The resilience of the cloud depends on the resilience of the physical world. If the physical world is unstable, the digital world will suffer. This reality forces companies to reconsider their architecture. They may need to decentralize their operations or invest in local sovereignty solutions.

Strategic Vulnerabilities in Multi-Region Architectures
Most enterprises use a multi-region architecture to ensure high availability. They assume that if one region fails, another will take over. This assumption is flawed in the face of widespread conflict. If multiple regions are located in the same geopolitical zone, they are all at risk. A single conflict can take down multiple regions simultaneously. This is known as a correlated failure. To mitigate this, companies must diversify their regions across different geopolitical zones.
However, diversification comes with its own challenges. It increases complexity and cost. Managing multiple regions requires more engineering resources. It also complicates compliance with local data sovereignty laws. Some countries require data to remain within their borders. Moving data across borders can violate these laws. Companies must navigate a complex web of regulations while maintaining security. The balance between compliance and resilience is delicate. Failing to comply can lead to legal penalties. Failing to maintain resilience can lead to business failure.
Building Resilience Against Geopolitical Disruption
To build resilience, companies must adopt a defense-in-depth strategy. This includes physical security, network security, and application security. Physical security involves hardened facilities and armed guards. Network security involves encryption and intrusion detection. Application security involves zero-trust principles. All three layers must be strengthened. Additionally, companies should invest in disaster recovery planning. This includes regular drills and testing of failover procedures.
Disaster recovery planning must account for physical destruction. Standard backups may not be enough. Companies need to store data in geographically diverse locations. They also need to ensure that their backup systems are not dependent on the same power grid. Redundant power sources, such as generators and batteries, are essential. These systems must be tested regularly to ensure they function when needed. The goal is to ensure that critical data is always accessible, even in the worst-case scenario.

The Path Forward for Enterprise Cloud Security
The path forward requires a shift in mindset. Security is no longer just about software. It is about the physical environment. Companies must collaborate with governments and local authorities to improve security. They must also invest in technology that can detect and respond to threats quickly. AI-driven security tools can help identify anomalies in network traffic. These tools can alert engineers to potential attacks before they cause damage.
Furthermore, companies should consider edge computing. By processing data closer to the source, they reduce reliance on central data centers. This reduces the risk of a single point of failure. Edge computing also improves latency for users. It allows for real-time decision-making even if the cloud is down. This is crucial for industries like healthcare and finance. These industries cannot afford downtime. They need systems that can operate autonomously when connectivity is lost.

Conclusion
The attacks on AWS infrastructure in the UAE and Bahrain are a wake-up call. They remind us that the cloud is not immune to physical threats. As the world becomes more interconnected, the risks associated with that connectivity increase. Companies must take these risks seriously. They must invest in resilience and security. They must also be prepared for the unexpected. The future of cloud security depends on our ability to adapt to a changing world. By taking proactive steps, we can protect our data and ensure business continuity. The time to act is now.




