Not long ago, obtaining a TLS certificate was a bureaucratic ordeal. A system administrator would manually generate a Certificate Signing Request (CSR), submit it through a web portal, wait for email-based domain validation, download the certificate, configure the web server, and then — crucially — remember to repeat the entire process 12 months later before the certificate expired. Multiply this across hundreds or thousands of endpoints in a modern enterprise, and you have a recipe for cascading outages, expired certificates, and exhausted operations teams.

The Automated Certificate Management Environment — ACME — was designed to eradicate this problem entirely. Standardized in RFC 8555, ACME is a protocol that allows clients and certificate authorities (CAs) to communicate programmatically, automating every phase of the certificate lifecycle: issuance, renewal, and revocation. Let’s Encrypt, launched in 2014 by the Internet Security Research Group (ISRG), brought ACME to the public internet at massive scale, issuing hundreds of millions of free, trusted TLS certificates and fundamentally reshaping the web’s security posture.
But ACME is not just for public web servers. Its clean, well-documented protocol model has made it an attractive choice for enterprise PKI deployments, private CAs, IoT device enrollment, and protocol translation layers that bridge legacy systems to modern certificate management workflows. This article explores ACME from a PKI engineering perspective — dissecting its protocol mechanics, its trust model, its challenge types, its implementation nuances, and how it compares to and integrates with established enterprise PKI approaches.
The ACME Protocol Architecture: RFC 8555 Under the Hood
At its core, ACME is a JSON-over-HTTPS protocol that enforces authenticated, stateful interactions between an ACME client and an ACME server (the CA). Every meaningful operation is signed using JSON Object Signing and Encryption (JOSE), specifically the JSON Web Signature (JWS) format. This ensures that requests cannot be tampered with in transit and are cryptographically bound to the requesting account.
The Directory and Nonce Model
The protocol begins with a directory endpoint — a well-known URL (typically /.well-known/acme/directory) that exposes the CA’s resource URLs as a JSON object. Clients discover endpoints for account creation, order submission, nonce retrieval, and revocation from this single document. This design enables version-agnostic client implementations: clients always start by querying the directory rather than hardcoding resource paths.
Anti-replay protection is enforced through nonces. Every POST request must include a fresh Replay-Nonce header value, obtained either from a HEAD /new-nonce request or from the Replay-Nonce header returned in the previous server response. The server rejects any request bearing a nonce it has already seen, preventing replay attacks even if a JWS-signed message is intercepted. This is a subtle but critical security control — it means that a leaked signed request cannot be replayed by an attacker to trigger unintended certificate issuance.
In a real-world implementation (as seen in enterprise ACME servers built on ASP.NET Core), the nonce pool is maintained in memory as a concurrent dictionary, invalidating entries upon first use. The server returns a fresh nonce in every response header, keeping the client’s nonce supply continuously replenished.
Account Management and External Account Binding
ACME accounts are created via a POST /new-account request, where the request body — signed with the client’s key pair — contains the client’s public key, agreement to terms of service, and contact information. The server responds with an account URL and an account object that acts as the persistent identity for subsequent operations.
For private or enterprise CA deployments, External Account Binding (EAB) is a critical security extension. EAB requires the ACME client to prove possession of a MAC key issued out-of-band by the CA operator before an account can be created. The client embeds a JWS-signed EAB token within the new-account request, and the server validates the MAC signature against its stored key. This gates account creation behind an administrative approval step — essential for CAs that need to enforce enrollment policies, charge for certificates, or link ACME accounts to organizational identities in an IAM system.
In enterprise implementations, the EAB delimiter and MAC key are commonly tied to a provisioned external account record, where the account’s organizational attributes (department, cost center, device owner) flow into the certificate’s Subject Distinguished Name or Subject Alternative Names via policy-driven mapping engines.
The Order Lifecycle: From CSR to Signed Certificate
The ACME order lifecycle is the central workflow of the protocol, and understanding it precisely is essential for anyone building or debugging an ACME implementation.
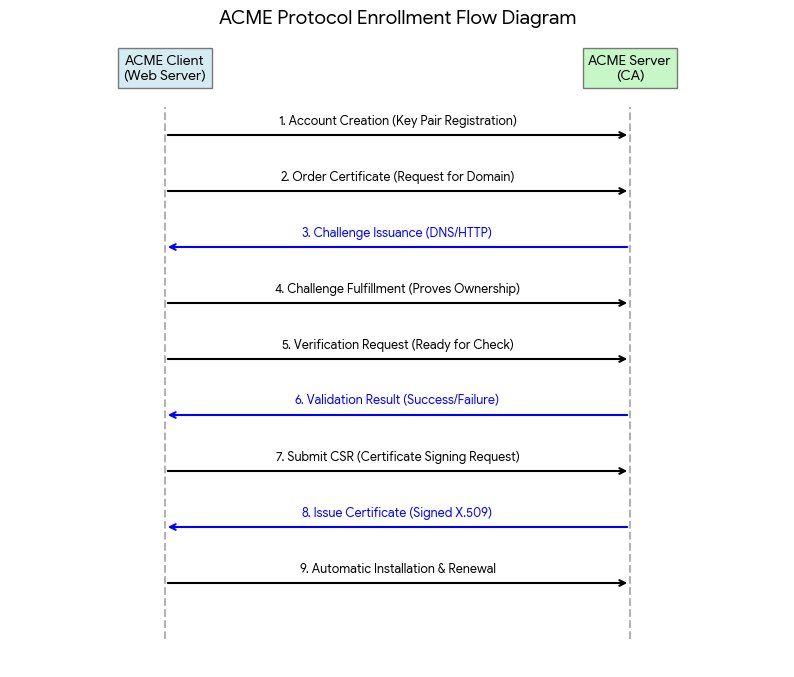
Step 1 — Submitting the Order
The client posts a new-order request listing the identifiers it wants to certify — typically DNS names, though ACME extensions exist for IP addresses and email S/MIME. The server creates an Order object in pending state and returns its URL along with a list of Authorization URLs, one per identifier, and a finalize URL.
Step 2 — Completing Authorizations and Challenges
For each identifier, the server provides an Authorization object containing one or more Challenge objects. The client must complete at least one challenge per authorization to prove control of the identifier. The three standard challenge types are:
- HTTP-01: The client places a key authorization token at http:///.well-known/acme-challenge/. The CA fetches this URL over port 80 and verifies the response matches the expected SHA-256 thumbprint of the account key.
- DNS-01: The client provisions a _acme-challenge. TXT record containing a base64url-encoded SHA-256 digest of the key authorization. The CA performs a DNS lookup to verify. This type supports wildcard certificates and works for domains unreachable from the public internet.
- TLS-ALPN-01: The client serves a self-signed certificate on port 443, negotiated via a special ALPN protocol identifier (acme-tls/1), embedding the key authorization in a custom X.509 extension. The CA connects and inspects the certificate.
The client signals readiness by posting to the challenge URL. The server transitions the challenge to processing, performs validation, and — upon success — marks both the challenge and its parent authorization as valid. If validation fails, the authorization transitions to invalid, and the order must be retried with a new nonce and fresh challenge tokens.
Enterprise ACME servers typically support configurable challenge type sets — for example, allowing only DNS-01 for wildcard orders and permitting both HTTP-01 and DNS-01 for single-name certificates. Wildcard DNS names (*.example.com) require DNS-01, as HTTP-01 validation is fundamentally incompatible with wildcard semantics.
Step 3 — Finalizing the Order
Once all authorizations are valid, the client generates a PKCS#10 CSR for the requested identifiers and posts it to the finalize URL. The server validates the CSR — checking that the identifiers match those authorized, that the key algorithm and length meet policy requirements, and that no prohibited extensions are present — and then submits the request to the underlying CA for signing.
The order transitions through processing to valid, at which point a certificate URL appears in the order object. The client downloads the signed certificate (and optionally the trust chain) via a POST-as-GET request to that URL.
Certificate Delivery Format
A correctly implemented ACME server returns certificates in PEM format. For chain delivery, the end-entity certificate is prepended to its issuing CA certificate(s), separated by newline characters. Clients that need DER encoding must convert client-side. In implementations built on BouncyCastle or .NET’s X509Certificate2, the PEM encoding can be reliably produced using PemEncoding.Write(“CERTIFICATE”, cert.RawData).
Let’s Encrypt: ACME at Internet Scale
Let’s Encrypt is simultaneously the most prominent ACME CA and the proof-of-concept that broke the commercial certificate industry’s stranglehold on basic web security. Operated by the ISRG as a nonprofit, Let’s Encrypt has issued over three billion certificates since its launch and secures roughly half of all HTTPS-enabled websites on the internet.

What Makes Let’s Encrypt Technically Distinctive
Several engineering decisions make Let’s Encrypt’s implementation particularly interesting from a PKI standpoint:
- Short certificate lifetimes. Let’s Encrypt issues 90-day certificates, deliberately shorter than the industry standard of 1–2 years at the time of its launch. The rationale is security hygiene: shorter lifetimes reduce the window of exposure for compromised private keys and encourage automation — since no sane operator wants to renew manually every 90 days. This design choice has since influenced the CA/Browser Forum to progressively shorten maximum certificate validity; as of recent proposals, maximum lifetimes may drop to 47 days by 2027.
- Certificate Transparency (CT) logging. Every certificate Let’s Encrypt issues is submitted to multiple CT logs before delivery. This makes issuance publicly auditable — any domain owner can monitor CT logs for unauthorized certificate issuance for their domains using tools like crt.sh or Google’s CT Monitor.
- Cross-signed root trust. Let’s Encrypt’s root CA (ISRG Root X1) was initially not trusted by all device certificate stores, particularly older Android versions. To achieve broad compatibility, Let’s Encrypt’s intermediate certificates were cross-signed by IdenTrust’s DST Root CA X3. Managing this trust chain transition — particularly when DST Root CA X3 expired in September 2021 — became a high-profile incident affecting millions of older Android devices, providing a vivid real-world lesson in PKI trust chain management.
- Boulder — the open-source CA. Let’s Encrypt operates Boulder, a fully open-source ACME server written in Go. Boulder enforces rate limits (50 certificates per registered domain per week, 5 failed validation attempts per account per hostname per hour, etc.) and serves as the reference implementation for ACME server compliance.
Popular ACME Clients for Let’s Encrypt
The client ecosystem around Let’s Encrypt is rich:
- Certbot — the canonical Let’s Encrypt client, maintained by EFF. Supports HTTP-01 and DNS-01 with dozens of DNS provider plugins.
- acme.sh — a pure POSIX shell script with extensive DNS provider support, popular in Linux/Unix environments.
- win-acme — the leading Windows client, integrating with IIS and supporting ACME EAB for enterprise CAs.
- LEGO — a Go-based client with strong DNS challenge support, commonly used in Kubernetes and containerized environments.
- cert-manager — the Kubernetes-native certificate management controller, supporting Let’s Encrypt and private ACME CAs through a declarative CRD model.
ACME in Enterprise PKI: Private CAs and Protocol Translation
While Let’s Encrypt demonstrated ACME’s power for public internet use cases, the protocol’s clean design has made it equally compelling for enterprise PKI environments where organizations operate private or managed CAs.
Why Enterprises Adopt ACME Internally
Enterprise PKI has traditionally relied on protocols like SCEP (Simple Certificate Enrollment Protocol), CMP (Certificate Management Protocol), or proprietary vendor APIs. ACME offers several advantages over these approaches:
- Standardization: RFC 8555 is unambiguous and well-maintained. Clients and servers from different vendors interoperate reliably.
- Rich client ecosystem: Organizations can leverage existing ACME clients rather than building custom enrollment agents.
- Automation-first design: ACME’s stateful order lifecycle and challenge model are designed for machine-to-machine operation, fitting naturally into CI/CD pipelines, Infrastructure-as-Code workflows, and service meshes.
- EAB for policy enforcement: External Account Binding allows enterprise CAs to gate enrollment behind organizational authentication — tying ACME accounts to LDAP identities, IAM roles, or device attestation records.
Protocol Translation Layers
A sophisticated pattern in enterprise ACME deployments is the protocol translation layer — a middleware component that exposes an RFC 8555-compliant ACME server interface to clients while translating requests into the native protocol of an underlying CA backend. This enables organizations to use modern ACME clients (Certbot, cert-manager, win-acme) against legacy CA infrastructure that does not natively speak ACME.

In such architectures, the ACME provider maintains its own order state machine — tracking accounts, authorizations, challenges, and order status in a concurrent transaction store — while delegating actual certificate signing to the backend CA via its native API (CMP, proprietary REST, PKCS#12 delivery, etc.). The protocol translator handles JWS validation, nonce management, challenge orchestration, and certificate format conversion independently of the backend CA’s capabilities.
The key engineering challenges in a protocol translation layer include:
- State synchronization: The ACME order state machine must remain consistent even if the backend CA request fails asynchronously. This typically requires a persistent order store with transactional semantics, not an in-memory dictionary alone.
- CSR validation and policy enforcement: Before forwarding a CSR to the backend CA, the translator must enforce naming policies — checking that requested Subject DN attributes and SANs comply with organizational rules, that prohibited OIDs are absent, and that key algorithm and length constraints are satisfied.
- Challenge delegation: For HTTP-01 and DNS-01 challenges, the translator must either perform validation itself or coordinate with DNS/HTTP infrastructure it controls. In private network deployments where the ACME server cannot reach client endpoints from the public internet, this often requires deploying challenge responder agents within the private network.
- Certificate chain assembly: The ACME protocol delivers the end-entity certificate and its chain as PEM-encoded data. The translator must correctly assemble the chain from backend CA responses, which may deliver certificates in DER, PKCS#7, or CMC formats, performing format conversion as needed.
Security Considerations: What Can Go Wrong
ACME’s automation benefits come with a specific threat model that implementers must understand deeply.
Key Compromise and Account Security
The ACME account is secured by the client’s key pair. If the private key is compromised, an attacker gains the ability to request and receive certificates for all identifiers previously authorized under that account. Mitigations include:
- Key rotation: ACME supports key rollover via a signed key-change request that atomically replaces the account key.
- Hardware security modules (HSMs): Storing the ACME account key in an HSM prevents extraction even if the client system is compromised.
- EAB key management: EAB MAC keys should be treated as credentials and rotated periodically. Their compromise allows unauthorized account creation.
Challenge Validation Risks
HTTP-01 and DNS-01 challenges have distinct attack surfaces. HTTP-01 is vulnerable if an attacker can serve content at the challenge path on port 80 — for example, by exploiting an open redirect or cache poisoning vulnerability on the target web server. DNS-01 is vulnerable to DNS hijacking attacks, particularly in environments with weak DNSSEC adoption.
Multi-Perspective Issuance Validation (MPIC), adopted by Let’s Encrypt and increasingly required by CA/Browser Forum policy, mitigates DNS-based attacks by performing challenge validation from multiple network vantage points simultaneously. An attacker would need to simultaneously hijack DNS responses from multiple geographically and topologically diverse locations to succeed.
Rate Limiting and Abuse Prevention
Public ACME CAs enforce rate limits to prevent abuse. Let’s Encrypt’s limits are well-documented, but they can catch legitimate users off guard during large-scale deployments. Engineers deploying ACME automation across many subdomains should design their enrollment workflows to stay well within rate limits, implement exponential backoff on failures, and use the ACME staging environment (which has relaxed limits) for testing.
Certificate Revocation in ACME
Revocation in ACME is performed via a POST /revoke-cert request, where the client submits the base64url-encoded DER certificate and a revocation reason code. The server validates that the requestor controls either the certificate’s private key or the associated ACME account, then submits the revocation to the CA backend.
ACME’s revocation reason codes map directly to the X.509 CRLReason values defined in RFC 5280 — including keyCompromise, caCompromise, affiliationChanged, superseded, cessationOfOperation, and unspecified. The semantics matter: keyCompromise (reason code 1) typically triggers immediate revocation and suppresses certificate hold eligibility, while superseded (code 4) may have different effects on OCSP responder behavior depending on CA policy.
A critical operational concern is the revocation propagation delay. Even after an ACME CA processes a revocation request, OCSP responders may serve cached good responses for up to their nextUpdate interval, typically hours. CRL distribution points may not be refreshed by relying parties for equally long periods. This means revocation in PKI is never instantaneous — a fact that must be communicated clearly to operations teams and factored into incident response playbooks.
Conclusion: ACME Is the Future of Certificate Automation
ACME has moved from a Let’s Encrypt-specific innovation to the dominant standard for automated certificate lifecycle management across both public and private PKI. Its well-defined protocol semantics, robust security model, rich client ecosystem, and extensibility through mechanisms like EAB and ACME ARI (Automated Certificate Renewal Information — a draft extension enabling CA-directed proactive renewal) make it the right foundation for any organization serious about certificate automation.

For PKI engineers and architects, the key takeaways are clear. Understand the JWS/JOSE trust model deeply — every security guarantee ACME provides flows from the integrity of account key management. Choose challenge types deliberately — DNS-01 for wildcards and internal names, HTTP-01 for simplicity where port-80 access is reliable. Treat EAB as mandatory for any private CA that must enforce enrollment policies. Design revocation workflows with propagation delays in mind. And embrace short certificate lifetimes not as a burden but as a forcing function for the automation discipline that modern infrastructure demands.
Let’s Encrypt proved that free, automated, ubiquitous TLS was achievable. ACME — as a protocol standard independent of any single CA — ensures that the automation it pioneered is available to every organization, whether issuing certificates for public websites, private microservices, machine identities in a Zero Trust architecture, or IoT devices enrolled at the factory floor. The era of manual certificate management is over. The era of ACME is well underway.



